BSides Delaware 2019
Talks
Preaching to more than just the choir: Working with developers to improve security
If we want to deliver secure products, security professionals need to learn to work closely with engineering teams & tools. In this talk I will discuss how engineering teams work, what motivates developers, and how to raise security concerns in w...
Yair Silbermintz
sec
CPE Sources: How to Make Your Life Easier
Obtaining your Certification is the first step. ISC2, ISACA, PMI all want you to continue learning. How many times have you gotten to October and realized you are struggling for CPEs? This is designed to help make your life easier by giving you op...
Bruce Dennis
sec
Retro Video Game Reverse Engineering
This talk will go over some results of reverse engineering certain retro video game software and hardware and what we can learn from the oversights of the past, as made on such constrained systems. On the software side we will look at how the spee...
@Theyflower, @StumpSpeedruns
sec
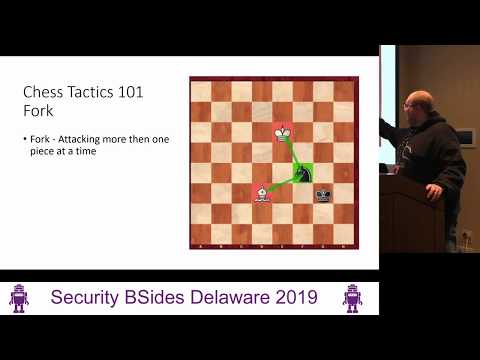
Basic Chess tactics for Fun and Bragging Rights
Learn the basics of chess including basic tactics that you can try on your friends and family. In this session we will go beyond various piece movement and explore concepts such as forks, pins, skewers, removing the defender, and central control. ...
Brandon Keath
sec
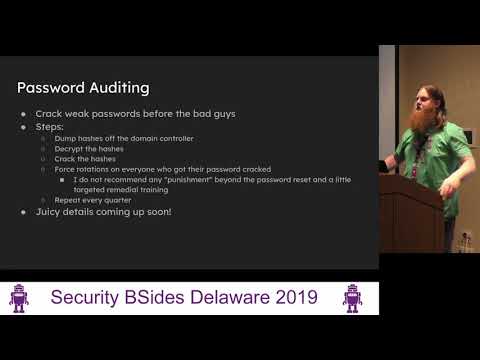
What I Wish I Knew About Password Auditing: Cracking User's Passwords before the Bad Guys
The goal of the talk is to give blue teamers and IT staff the knowledge they need to do internal audits of their Active Directory credentials and to dramatically increase the difficulty of attacks that abuse passwords such as password spraying and...
Ben Tice
sec
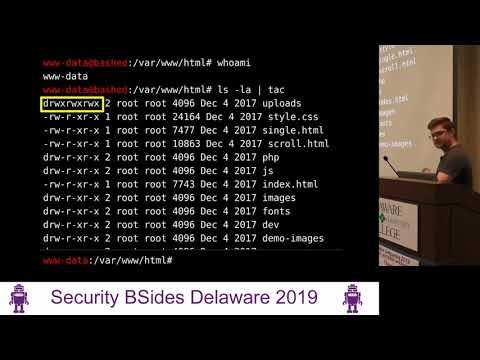
A Poor Man's Pentest: Automating the Manual
So you have popped a shell, and now you have to deal with the same tedious boilerplate and manual interaction on your target that you always do. You run the same commands to stabilize your shell, you setup the same persistence implants as usual, a...
John Hammond
sec
Dissecting Carbanak
Even though the Carbanak Source Code dump has been around for a while, not much information has come out that breaks down the compilation steps and source code analysis of the dump. In this talk, I will walk through my journey of getting Carbanak ...
Hristo Aseno
sec
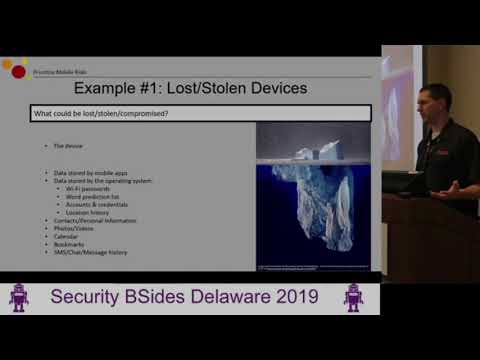
What Should a Mobile Security Program Look Like? YMMV...
So, you want the perfect mobile security program for your company/organization? Great! Just know that your set of threats, priorities and limitations will ensure that it probably won’t look like the one created by the person next to you. In this t...
Jeff Hague
sec
Exploiting IoT - An Introduction to BLE
BLE is one of the most common wireless protocols used in IoT devices today. This talk will follow the BLE protocol and apply a 4 phases approach to assessing the security of these devices: Reconnaissance, Sniffing and Capturing, Extracting Sensiti...
Charles Sgrillo
sec
Matching Your SOCs: A Discussion of Joint IT/OT Operating Models for Monitoring and Response
Traditional security monitoring and response operations are not sufficient to combat the evolving cybersecurity threat landscape for Operational Technology (OT). While the advancement in tools and technology is helpful, the tools alone will not en...
Trevor Houck
sec
Our Adventure with an Awareness Training Escape Room
Are you as tired of Annual Awareness Training as your users are? It might be time to change up your approach to Security Awareness Training with some gamification. Escape Rooms can be fun and a great opportunity for team building while demonstrati...
Bob Hewitt
sec