BSidesSF 2020
Talks
How To Write Like It's Your Job
Hackers thought they could avoid formal essays, but SURPRISE! They still have to write about exploits. And writing is hard. But it's ok, I'm here to help with practical advice for security writers - how to start and finish, tools to consider, and ...
Brianne Hughes
Security
How The Coasts Approach Information Security Differently
How Wall Street and Silicon Valley fundamentally differ in their approaches to information security, and what one can learn from the other...this talk will be useful to the assessor/auditor, the advisor, the operator and anyone generally intereste...
Sourya Biswas
Security
How to 10X Your Company’s Security (Without a Series D)
I’ll summarize and distill the insights, unique tips and tricks, and actionable lessons learned from a vast number of DevSecOps/modern AppSec talks and blog posts, saving attendees 100s of hours. I’ll show where we’ve been, where we’re going, and ...
Clint Gibler
DevOps
DevSecOps
Security
Phishy Little Liars - Pretexts That Kill
The 'IT Guy' is the Nigerian Prince of Pretexts. As bad actors begin to use more specialized pretexts, so too should Pentesters use more specialized, custom pretexts during assessments. Learn to make custom pretexts that fly under the radar and wo...
Alethe Denis
Security
Transform Your Presentation Skills
Are you conference ready? Do you want to give a presentation that everyone is talking about? Then check out Transform your Presentation Skills for unique tips and tricks that will result in compelling content and improved confidence. Bay Area pres...
Hilary Spreiter, Anne Ricketts
Security
What Should and Shouldn’t Scare You: Kubernetes and Containers
Kubernetes and containers change a lot of how apps are built, deployed, and secured… or do they? Let’s cut through the hype and see what’s same-old-same-old versus actually new, then talk about the chance we’ve got to do security better together. ...
Connor Gilbert
Kubernetes
Security
Panel: Let's Get 360 With Bug Bounty!
From bug bounty hunters, to the platform triagers, to the companies that fix the vulnerability: we have much to understand and learn from each other. We will talk about the bug bounty lifecycle from multiple perspectives and discuss how to improve...
Jeff Boothby, Chloé Messdaghi, Tanner Emek, Maria Mora, Ben Sadeghipour
Security
Hanging on the Telephone: Hacking VoIP
Sarah details some of the ways that VoIP systems can be hacked and used for nefarious purposes.
Sarah Young
Hacking
Security
Serverless Osquery Backend and Big Data Exploration
osquery is an open-source community driven endpoint for intrusion detection. Deploying at scale requires endpoint management, data transport and additional considerations. We'll deploy a serverless osquery backend, discuss the challenges at scale ...
Geller Bedoya
Security
Serverless
Peeling the Web Application Security Onion
Bruce Schneier said security is a process, not a destination. This talk focuses on web app security aspects in the browser, CDN or API Gateway, Static Content Servers, and Dynamic Web Services. It shows how you can better mitigate risks in the mul...
Noam Lorberbaum, Keith Mashinter
Security
Adventures in Vendor Security and Continuous Review
The advent of cloud services has created a new paradigm in vendor security. Typically, companies send a questionnaire to review cloud providers, however, it's point in time. The attendees will learn about methods of identifying security posture of...
Lokesh Pidawekar
Security
The GCP Metadata API
Some folks know about the AWS metadata API and its security implications. Here I'll talk about the GCP metadata API and its security implications. GCP has extra protections, but a lot more at stake. I'll cover ways to attack and defend the GCP met...
Dylan Ayrey, Allison Donovan
GCP
Security
Ask the EFF
This session will include updates on current EFF issues such as surveillance online, encryption (and backdoors), compelled decryption, consumer privacy, free speech, and right to repair. The panel will also include a discussion on some exciting ne...
Jamie Williams, Kurt Opsahl, Hayley Tsukayama, Alexis Hancock
Security
Keynote: What's New or Not in 2020: Are we Making Progress?
It's the end of the decade and time to look back on which parts of the mission of Information Security professionals have progressed and which are still just treading water. As we come together for the first BSidesSF of a new decade, have security...
Larkin Ryder
Security
Creating Threat Intelligence Signals in a “Zero Trust” Environment
As network architecture changed over the years, threat intelligence in a “Zero Trust” environment should be re-shaped into a dynamic signal-based indicator of threats that are associated with organization entities and empowered by a variety of dat...
Or Katz
Security
Visualizing Security
Data analysis and visualization skills are becoming a critical part of the security domain. To learn what makes for good analysis and visualizations, this talk will share and explore real-world security analyses and visualizations (and animations)...
Jay Jacobs
Security
How to Kill an AWS Access Key
AWS Access Keys are great for attackers; powerful and sitting in plaintext. The Security Token Service enables short-lived credentials, but the path to getting that to work for humans isn't simple. Assuming zero level of expertise, we'll cover how...
Benjamin Hering
AWS
Security
A Look at Jython-Enhanced Reverse Engineering with Ghidra
Tired of long days spent reversing obfuscated binaries that want nothing more than to make your life miserable? Then look no further! Using real-world malware as a case study, I'll show how to use Jython and Ghidra's powerful scripting API to make...
Byron Roosa
Jython
Security
Keynote: Dumping Traditional Security Teams
It’s common to hear of security teams that feel overwhelmed. They have too many alerts, too many design reviews, too many approvals, too many everything! What if I told you we can reduce risks and scale security by reducing what security teams do?...
Fredrick Lee
Security
Securing Coinbase’s Edge Payments Infrastructure
Coinbase works with payment processors across the globe. We have seen a lot of insecure APIs. Interested in seeing what problems are in these payment networks that move billions of dollars daily and how Coinbase remediates these issues using commo...
Nishil Shah
Security
MOSE: Using Configuration Management for Evil
Ever land on a configuration management server and not know what to do? Want to take over machines en masse with a single command? Enter Master Of SErvers (MOSE), a post-ex tool that allows you to leverage CM servers to compromise all associated a...
Jayson Grace
Security
Leveraging Osquery for DFIR at Scale
Security Breaches are happening every other week - understanding the anatomy of an attack is a daunting task that Incident Responders face. Attackers will leave behind breadcrumbs. Forensics tools can be time & resource intensive. Can we explore a...
Sohini Mukherjee
Security
Mapping the Connections Inside Russia’s APT Ecosystem
This talk will detail the stages involved in the research study of the analysis of the Russian APT ecosystem. It will present two open-source tools which can be used by the infosec community to further investigate Russian-related cyber attacks.
Ari Eitan
Security
Graph Based Detection and Response with Grapl
Grapl is a Detection and Response Platform that centers around graph analytics services. By leveraging Graphs and Python Grapl makes it easier to build more powerful, behavior-oriented attack signatures and explore suspicious behaviors in your env...
Colin O'Brien
Security
San-Serif Rules Everything Around Me
Lowercase L and uppercase i look exactly the same when used in Sans-Serif fonts. Apple iMessage, Gmail, Facebook, and Twitter all display urls in mixed case San-Serif fonts. This opens up the potential for very simple and highly effective phishing...
Travis Knapp-Prasek
Security
Managing the Assets of Your Security Career
Security folks often struggle with quality feedback and influence during promotion. In this session I provide tooling and strategies for “asset management” of stakeholders that will improve the growth of influence, increase visibility in an organi...
Chris John Riley, Kyle Tobener
Security
Real Time Vulnerability Alerting
Harness public data and apply data analytics principles from US Tsunami Warning Center to cut through the noise and get real-time time alerts only for highly seismic vulnerabilities. Make vulnerability fatigue a thing of the past.
Amol Sarwate
Security
Purple is the New Black: Modern Approaches to Application Security
This talk will explore how to combine defence, offence, automation, empathy and continuous learning in a MODERN approach to application security. All new types of applications will be covered as well as their corresponding security best practices.
Tanya Janca
Security
Developing a Baseline Security Standard for Endpoint Devices
As part of implementing a Zero Trust Network, we sought to ensure that endpoint devices met a baseline security capability standard. The goal was to document the OS security capability posture, and map those functionalities to the baseline to dete...
Claire Moynahan
Security
From Cockroaches to Marble Floors
Eliminating the false distinction between security bugs and other software defects can greatly reduce the risk of security breaches, improve product quality and align builders around the same goals. We'll present practical tools & methodologies th...
Daniel Tobin, Paul Karayan
Security
k-rail: A Tool to Manage K8s Securely at Speed
Kubernetes is powerful, but often insecurely configured. During this talk, we’ll roleplay offensive and defensive scenarios we’ve learned in our journey of running Kubernetes at Cruise and share the tool we’ve created to mitigate them.
Dustin Decker
Kubernetes
Security
The Voight-Kampff Test for Discovering Vulnerabilities
Among the thousands of vulnerabilities you find, how can you tell which were found through automated scanners and which required human expertise? We'll build a Voight-Kampff test to filter between human-found and machine-found vulns.
Vanessa Sauter
Security
Secure by Design: Usable Security Tooling
How do you build effective security products? Are people actually using your tools? Spending time on usability for security products is a smart investment with high payoffs. In this talk we’ll discuss how prioritizing usability allows us to build ...
Hon Kwok
Security
Dispatch: Crisis Management Automation
We built Dispatch to automate our entire crisis management lifecycle, from initial report, to resource creation, participant assembly, task tracking and post-incident reviews. We want you to use it someday too, so we'll explain how it helps us, an...
Forest Monsen, Marc Vilanova
Security
Mistakes Made Integrating Security Scanning into CI/CD
It was 8AM, Slack showed 124 new unread messages and climbing. Our security scanner had broken every build pipeline. Do you want to know why? Are you curious to know the steps we took to bounce back? Do you want to learn from our mistakes?
Moses Schwartz, Atul Gaikwad
Security
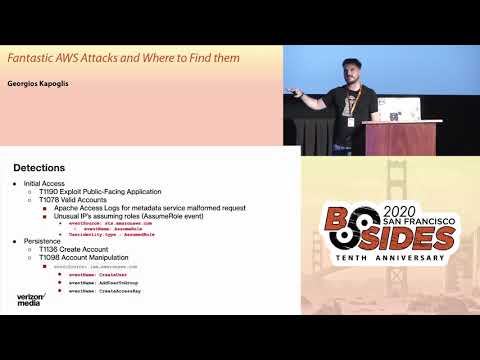
Fantastic AWS Attacks and Where to Find Them
Building better detections on our Cloud infrastructures and knowing our enemies is a necessity for survival. I want to help the community by sharing our work on AWS and by utilizing ATT&CK framework start building and operationalizing detections a...
Georgios Kapoglis
AWS
Security
Sharks in the Water: Open Source Component Risk and Mitigation
Navigating the Open Source Component (OSC) Supply Chain can be murky and unforgiving. Gain an understanding around how recent hacks could have been prevented by proper management of OSCs through education, awareness, and automated tooling.
Aaron Brown
Security
How Software Transparency Can Help Save the World
“Am I affected by this new vuln?” This is a question very few orgs that make or use software can answer today, since we lack visibility into the software supply chain and the full set of dependencies. Learn how a “software bill of materials” or SB...
Allan Friedman
Security
Security Learns to Sprint: DevSecOps
This talk will explain what security teams needs to adjust in order to turn DevOps into DevSecOps within their organizations. Several strategies are presented for weaving security into each of the "Three Ways", with clear steps audience members ca...
Tanya Janca
DevOps
DevSecOps
Security
Panel: Mental Health for Hackers
Pressures and stress affect both professional and personal lives within infosec. This panel will introduce mental health for hackers, and discuss issues including burnout, depression, anxiety and other topics. The conversation will help build a su...
Chloé Messdaghi, Ryan Louie, Susan Peediyakkal
Security
Bootstrapping Security
Bank of America has publicly shared that they spend over $400M per year on cybersecurity and that cybersecurity is the only department without budget constraints. Unfortunately, most of us have budgets many orders of magnitude smaller than that. S...
Rob Shaw, Jared Casner
Security
Closing Ceremony
We will be discussing the logistics and joys of organizing the event. Come hear how it all gets put together and who helps us out!
Reed Loden
Security
Privacy Nightmares while Using ML/AI
Everyone is excited with using ML And AI in applications but what about privacy while mining personal data within applications? See privacy nightmares can happen without due care. We aim to address issue by introducing a framework that blends ML a...
Yogesh Karpate, Sameer Ahirrao
Machine Learning
Security
RIS-ky Business: Exploiting Medical Information Systems
The security of medical devices has been a hot topic in the news the past few years. This presentation gives an overview of medical specific protocols, the architecture of a medical information system, and how an attacker can leverage these to cha...
Jacob Brackett
Security
CISO Vendor Relationship Podcast
Join David Spark, Mike Johnson, and guest Olivia Rose for 45 minutes of the most fun you’ll have at BsidesSF 2020. The CISO/Security Vendor Relationship Podcast is couples therapy for security practitioners and vendors. We’ll debate hotly conteste...
Mike Johnson, Olivia Rose, David Spark
Security
An Effective Approach to Software Obfuscation
Understanding the essential aspects that make up obfuscation allows us to see the fundamental flaw with modern obfuscation implementations and the right way to approach it. We use examples of modern obfuscation techniques to illustrate our points ...
Yu-Jye Tung
Security
Non-Political Security Learnings from the Mueller Report
The Mueller Report had a trove of forensics evidence around how the DNC & DCCC were compromised. By reading the Report through a critical security lens we can gather a trove of learnings around how access was gained, how their networks were traver...
Arkadiy Tetelman
Security
Lessons from DevSecOps Trenches
A frank discussion with security team leads at several forward-thinking companies on how they’ve built and scaled their security programs. What worked, what failed, and more. No topics are off-limits, no holds will be barred, and chanting will be ...
Astha Singhal, Doug DePerry, Zane Lackey, Justine Osborne, Clint Gibler
DevOps
DevSecOps
Security
When GDPR and CCPA strike
Data protection obligations can be an ally to the security team instead of a burden. Having a good understanding of them helps inform security risk modeling and prioritization, secure buy-in when setting the agenda of a security program, and reduc...
Rafae Bhatti
Security
Break Crypto like a Pro!
Cryptography is hard. Doing it right is even harder, and Murphy’s law continues to prove true: “If there is a wrong way to do something, then someone will do it.” Come learn how to exploit common crypto mistakes in theory and in practice!
Alexei Kojenov
Security
Security, Politics, Neutrality, and Protecting Users
Tech's alleged "neutrality" causes security problems for our users--ranging from misinformation and propaganda to harassment and worse. Is neutrality required, or desirable? Should tech itself (as Microsoft once suggested) be sovereign? What happe...
Brendan O'Connor
Security
2FA in 2020 and Beyond
This talk will explore the modern landscape of 2FA. With a data driven analysis of the tradeoffs between different types of factors, we'll dive into a detailed comparison of cryptographic security strength and UX for methods like SMS, Soft Tokens,...
Kelley Robinson
Security
Chrome Extension Risks and You
An often overlooked risk in Google Chrome are the thousands of unique Chrome extensions installed by your users. We will cover examples of risky and malicious (sometimes popular) extensions and share how Lyft strategically reduced risk at scale wi...
Chris Barcellos, Abhi Kafle
Security
So You’re the First Security Hire
You're the first security hire at a company, where do you start? How do you keep the company from getting hacked without getting in the way? How do you integrate security into the culture of the business? I'll cover the critical areas to focus on,...
Bryan Zimmer
Security
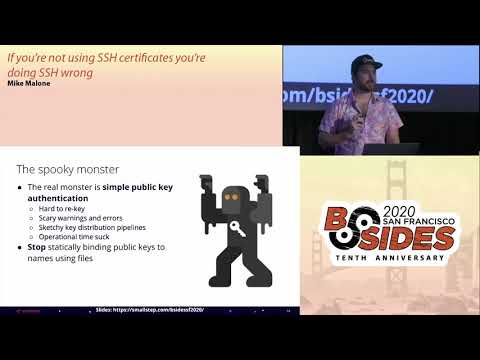
If You’re Not Using SSH Certificates You’re Doing SSH Wrong
Lightning Talk - Based on a popular blog post of the same name (over 50,000 unique views in the first 30 days) this lightning talk challenges the listener to reconsider using keys for SSH access, and instead use SSH Certificates. https://smallstep...
Mike Malone
Security